⭐⭐⭐⭐⭐ Trusted by 14 Million Users Worldwide
Try Risk-Free for 30 Days
Cancel anytime — no questions asked.
Our #1 recommended VPN for your device, now 68% off
Deal could end tomorrow — Don't miss out
Why VPNs Matter in 2026
Your privacy, security, and access online are shaped by the numbers below.
VPN Speed Lab
Your single truth for unbiased speed metrics performed by our cloud network tests. Learn more
Get access to exclusive offers.
Bigger savings = more money in your pocket.
Terms apply. Offers may change.
A VPN is one of the most powerful tools for protecting your online privacy, securing sensitive data and accessing the internet without restrictions.
Every time you browse the web, your activity can be tracked by your internet service provider (ISP), websites and even attackers on public networks. A VPN solves this by encrypting your connection and hiding your identity.
What is a VPN?
A VPN is software that encrypts your internet traffic and hides your real IP address by routing your connection through a private server. This keeps your online activity private and lets you browse as if you’re in a different location entirely.
For a complete technical breakdown, see our guide on what a VPN is and how it works.
Why You Need a VPN?

VPNs solve five critical problems that affect every internet user:
- Public Wi-Fi protection: Unsecured coffee shop and airport networks expose your passwords, banking credentials, and messages to nearby hackers in real time. A VPN encrypts everything, making it unreadable even on compromised networks.
- ISP privacy: Your internet provider logs every site you visit and sells that data to advertisers and data brokers. A VPN hides your browsing activity from your ISP, keeping your online habits private.
- Streaming access: Geo-blocks prevent you from watching your shows while traveling abroad. The best VPN for streaming lets you connect to a server in your home country, making it appear you’re still there and unlocking access.
- Bandwidth throttling prevention: Some ISPs intentionally slow your connection speed during peak usage. A VPN hides what you’re doing online, so your ISP has no reason to throttle your connection.
- Remote work security: When you work from public locations or use unfamiliar networks, accessing company files and systems is risky. A VPN encrypts all work-related traffic, protecting sensitive data from interception.
VPN vs Proxy vs Tor: Key Differences
VPNs, proxies and Tor all hide your IP but work differently and suit different needs. Our VPN vs proxy guide breaks down the key differences, including when you’d choose one over the other.
How Does a VPN Work?
When you activate a VPN, your connection is encrypted and routed through a private server; the website you visit sees the server’s IP, not yours. Our VPN setup guide covers installation on every device.
How to Choose the Right VPN?
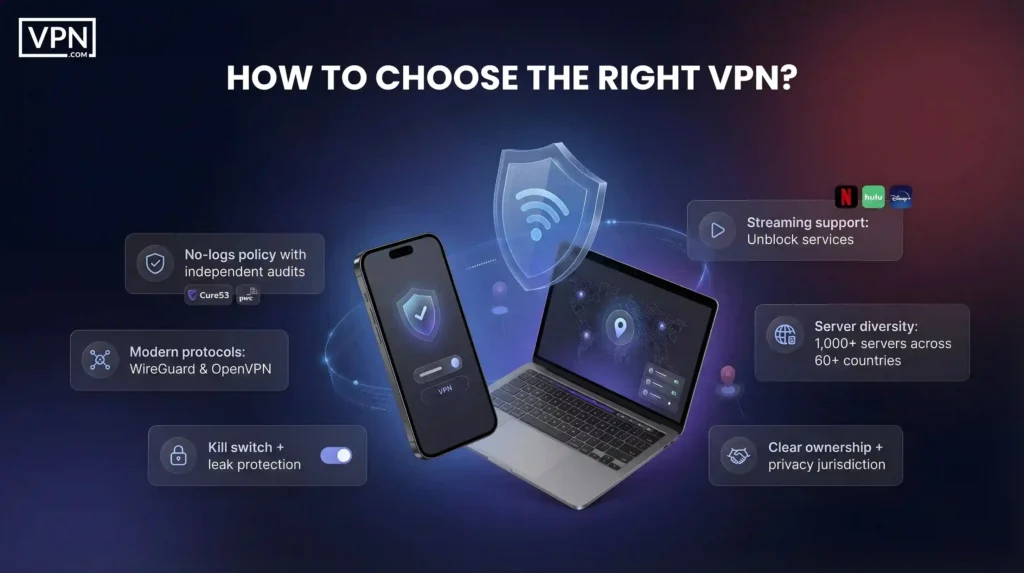
The most important factors when choosing a VPN (from no-logs audits to kill switches and jurisdiction) are covered in our “How to Choose a VPN” guide.
For specific use cases, see:
VPN Speed Testing: Real-World Performance
We’ve tested 50+ VPN providers using our Speed Lab methodology. Here’s how the top performers compare on a 1 Gbps fiber connection:
| VPN Provider | Download Speed | Speed Retention | Latency Increase |
| NordVPN | 730 Mbps | 73% | +12ms |
| Surfshark | 680 Mbps | 68% | +15ms |
| ExpressVPN | 650 Mbps | 65% | +18ms |
Modern VPNs using WireGuard add only 5–15% latency on broadband connections. The privacy benefit far outweighs the minor speed reduction for most users.
VPN Security & Privacy: What You Should Know
A VPN is a strong privacy tool, but it has important limits. Understanding what it protects and what it doesn’t is critical.
A VPN protects you from:
- Your ISP sees which sites you browse
- Hackers on public Wi-Fi are stealing your passwords
- Websites identifying your real location
- Your activity logs are being sold to advertisers
A VPN does not protect against:
- Malware or viruses on your device
- Phishing attacks that trick you into giving up information
- Browser fingerprinting techniques
- Third-party cookies and tracking pixels
A VPN works best as part of a broader security strategy that includes strong passwords, two-factor authentication and reputable antivirus software. For complete online security guidance, see our cybersecurity hub.
It’s also worth knowing where VPNs are legal before relying on one.
Best VPNs: FAQs
The Bottom Line
A VPN encrypts your data, hides your IP address and protects your privacy on any internet connection. For public Wi-Fi security, streaming access, remote work and everyday browsing, a VPN is one of the best security investments you can make.
Choose a service with modern encryption (AES-256), a proven no-logs policy backed by audits and servers in locations you actually need. Test one with a money-back guarantee to see how it fits your life.
Ready to protect your privacy? Compare top-rated VPN providers and find the right service for your needs.