⭐⭐⭐⭐⭐ Trusted by 14 Million Users Worldwide
Try Risk-Free for 30 Days
Cancel anytime — no questions asked.
Our #1 recommended VPN for your device, now 68% off
Deal could end tomorrow — Don't miss out
Why VPNs Matter in 2026
Your privacy, security, and access online are shaped by the numbers below.
VPN Speed Lab
Your single truth for unbiased speed metrics performed by our cloud network tests. Learn more
Get access to exclusive offers.
Bigger savings = more money in your pocket.
Terms apply. Offers may change.
A VPN is a powerful tool for cybersecurity. It helps keep your online actions safer and more private. Let us explain everything you need to know about VPNs and why using one makes sense.
| VPN | From (2-year plan) | Countries | Devices | Jurisdiction | Our Review |
| NordVPN | $3.39/mo | 178 | 10 | Panama | See More Details |
| ExpressVPN | $3.59/mo | 105 | 10 (Basic) | BVI | See More Details |
| CyberGhost | $2.03/mo | 100 | 7 | Romania | See More Details |
| Surfshark | $1.99/mo | 100 | Unlimited | Netherlands | See More Details |
| PIA | $1.98/mo | 91 | Unlimited | USA | See More Details |
Along the way, if you want to know how we test VPNs, check speed, security, and reliability. We share tips to help you pick the right VPN.
- Here is our testing methodology.
What is a VPN?
A VPN, or virtual private network, is a tool that protects your internet connection and boosts your online privacy. It uses encryption, which is a smart way to scramble your data so snoopers and hackers cannot read it. Even if someone catches your traffic, they see only meaningless information.
For a step-by-step explanation, see how VPN encryption works.
Besides encrypting your data, a VPN also hides your real IP address and your location. For example, when you connect to a server in another country, websites believe you are browsing from that place. Using a VPN is legal in most countries as long as you avoid illegal activities. Governments, businesses, and millions of regular people use VPNs every day to stay more secure and keep their privacy strong.
In recent years, WireGuard has become a popular alternative to older VPN protocols. WireGuard is simpler, faster, and more secure. It relies on up-to-date cryptography and delivers better performance than older protocols like PPTP or L2TP/IPsec.
How to Choose the Best VPN (Checklist)
- No-logs policy with independent audits
- Modern protocols (WireGuard preferred + OpenVPN backup)
- Kill switch + full DNS/WebRTC leak protection
- Streaming support (Netflix, Hulu, Disney+, etc.)
- P2P/torrenting allowed with fast dedicated servers (if needed)
- Servers in locations useful to you (nearby for speed, specific countries for content)
- Clear company ownership + regular transparency reports
VPN vs Proxy
Both VPNs and proxies hide your real IP address by routing your traffic through a middle server. But they work differently and suit different needs. Let us explain the key differences so you can decide which one best fits you.
A proxy acts like a simple relay. It changes your IP for the sites you visit, but does not encrypt anything. Your data stays visible to your ISP or anyone who intercepts it. Proxies work well for basic tasks, such as watching a blocked video in your browser, but leave you exposed otherwise.
| Feature | VPN | Proxy |
| Encryption | encrypts all your data | No or very limited, usually none |
| Privacy & Security | Hides activity from ISP hackers | Only hides IP & no data protection |
| Coverage | Protects your every device and all apps | Mostly browser or one app only |
| Speed | Slightly slower due to encryption | Usually faster & no heavy encryption |
| Use Cases | Public Wi-Fi privacy, torrenting, streaming & remote work | Quickly unblock data & simple browsing |
| Cost | Mostly paid good ones $3-10/month | Many free but risky paid ones are available |
| Reliability | Stable connections & strong no-logs options | Can drop more often & free ones are unreliable |
In most cases, a VPN is the better choice if privacy or security matters to you. Free proxies often log sell data or add ads. Modern VPNs with WireGuard offer fast speeds and strong protection with minimal slowdown.
Quick tip: Use a proxy only for light tasks where speed trumps security. Go with a trusted paid VPN for everything else. Test one with a money-back guarantee and see how it feels.
Learn the key differences in our proxy vs VPN guide.
VPN vs Tor
Both VPNs and Tor help hide your online activity and protect your privacy, but they work in very different ways.
Tor the Onion Router bounces your traffic through volunteer-run relays. Each relay peels off one layer of encryption, so no one sees the full path. This gives stronger anonymity against powerful trackers, but it is much slower and not ideal for video or large downloads, and exit nodes can sometimes snoop unencrypted traffic.
| Feature | VPN | Tor |
| Routing | One trusted server | 3+ random volunteer nodes |
| Encryption | Strong full-device | Layered multi-hop |
| Speed | Fast | Very slow |
| Anonymity | Good | Excellent |
| Privacy from Provider | Depends on the no-logs policy | No central provider |
| Coverage | All apps & devices | Mostly Tor Browser |
| Best for | Daily use | Maximum anonymity or to access the dark web |
| Cost | Paid | Free |
| Ease of use | Simple app | More technical |
| Reliability | Stable | Can be unreliable, risky exit nodes |
The best VPN service with WireGuard offers the best balance of speed, security, and ease. Tor is great when you need the highest possible anonymity, like accessing the dark web or evading heavy censorship, but expect patience with speed.
Quick tip: Use a VPN for everyday privacy and safety. Switch to Tor only when absolute anonymity matters most. You can even combine them like VPN first, then Tor for extra protection, but it slows things down more. Test both and see what fits. Stay safe online.
Why Do You Need a VPN?
The best VPN gives you several real benefits that make it worth using if you spend time online. Let me walk you through the main reasons why it makes sense to have one.
It Keeps You Safe on Public Wi-Fi
Public Wi-Fi spots often leave your information open to hackers. Think of it as an unlocked door. A VPN steps in by encrypting your data so anyone trying to peek sees only scrambled nonsense, not anything useful.
Here’s a quick guide to staying safe on public Wi-Fi.
It Lets You Reach Blocked Content
Have you ever tried to watch your favorite show while traveling, only to find it unavailable? Streaming services limit content based on your location because of licensing rules.
A VPN changes that. You connect to a server in your home country, and suddenly, those shows and movies become available again, no matter where you are.
It Stops Your ISP from Watching You
Your internet provider logs every site you visit. They often sell that information to advertisers or share it with others. A VPN sends your traffic through an encrypted server first. Your ISP sees nothing about your browsing, which keeps your habits private.
It Ends Bandwidth Throttling
Sometimes your connection slows down during gaming or streaming because your ISP may be using internet throttling when it detects heavy use. A VPN hides what you are doing online. Since your ISP cannot tell if it is gaming or video, they have no reason to slow you down. You get smoother play without sudden lag.
It Protects You During Remote Work
More people work from home or elsewhere these days. You often need to access company files online. On public Wi-Fi, that can be risky if a hacker is nearby. A VPN encrypts everything, so you can safely open work documents and networks without fear of leaks or breaches.
How Does a VPN Work?
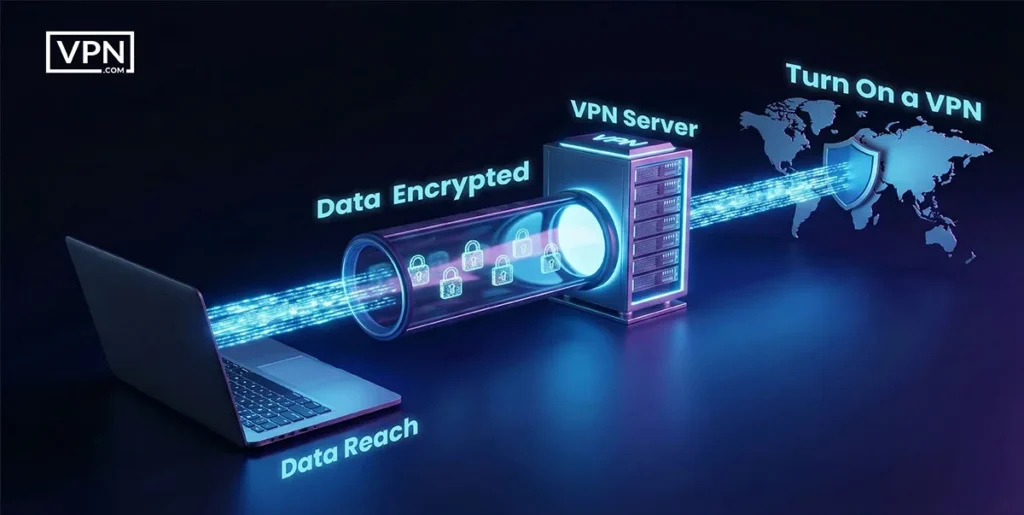
A VPN works by creating a private connection between your device and the internet. This connection controls how your data travels online and who can see it. Without a VPN, your internet traffic moves openly across networks. With a VPN, your activity is protected from the moment you connect.
What Happens When You Turn On a VPN
When you turn on a VPN, the app connects your device to a secure network. This happens before your data reaches your internet provider or any public Wi Fi network. Your real connection is replaced with a protected one. Every request you make online is sent through this secure path instead of going directly to the internet.
How Your Data Gets Encrypted
Encryption is the core of how a VPN works. The VPN encrypts your data. This code cannot be read without the correct key. Even if someone intercepts the data, they cannot understand it. This keeps your login messages and browsing activity safe at all times.
The Role of the VPN Server
The VPN server acts as a safe gateway to the internet. Your encrypted data goes to this server first. The server then forwards the request to the website you want to visit. The website only sees the VPN server information. Your real IP address and location stay hidden behind it.
How the Data Reaches the Website
After the VPN server contacts the website, it receives the response. That response travels back to the VPN server and then to your device. The data remains encrypted until it reaches you. This secure loop works continuously while the VPN is active.
This process protects your privacy and gives you more control online. It helps prevent tracking and spying. It also reduces risks when using public networks. A VPN does not change how you browse. It simply makes your internet use safer and more private at every step.
What Are the Different Types of VPNs?
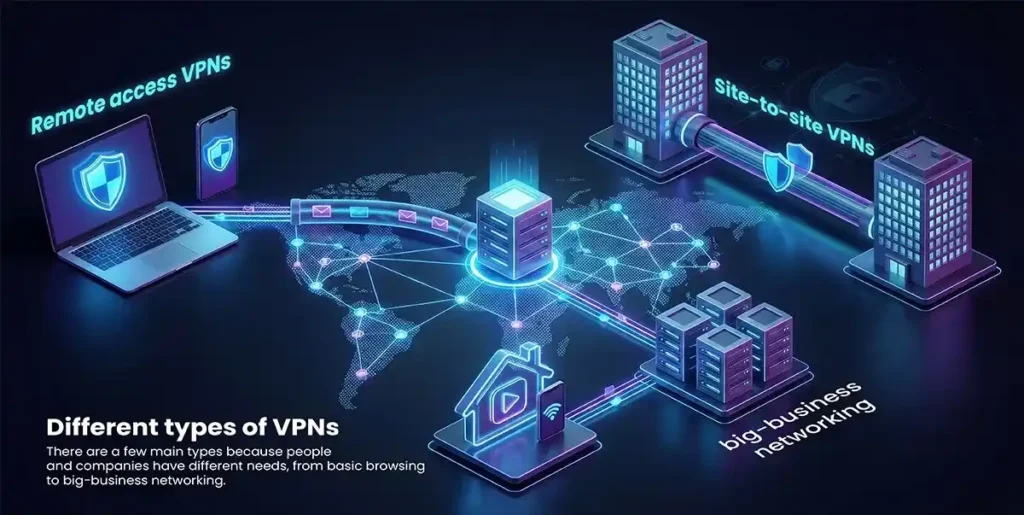
There are a few main types because people and companies have different needs, from basic browsing to big-business networking. Let us explain the key ones so you can see which might fit you best:
Remote Access VPNs
These VPNs let your personal devices connect directly to a private network. Your devices mean things like your phone, laptop, or computer. You usually open a VPN app, browser extension or desktop program, type in your login details and you are connected.
Remote-access VPNs work well for people who work from home or travel. They need to reach the company’s file systems or tools safely from anywhere outside the office.
Site-to-Site VPNs
These are built for big companies with offices in many locations. Instead of linking individual devices, a site-to-site VPN connects entire networks across locations. It lets workers in different branches share files, printers, and other resources easily.
Everyone feels like they are on one big local network, even though they are miles apart. Think of it as a secure bridge that ties company offices over the internet.
Consumer VPNs
This is the type most people picture when they hear about VPNs. Consumer VPNs focus on normal daily use like watching shows, browsing the web, or playing games. They do not connect you to a work network. Instead, they send your internet traffic through their own servers to hide your activity and location.
Many individuals choose them to stay private online or unlock shows and sites blocked in their country.
How Secure Is a VPN?
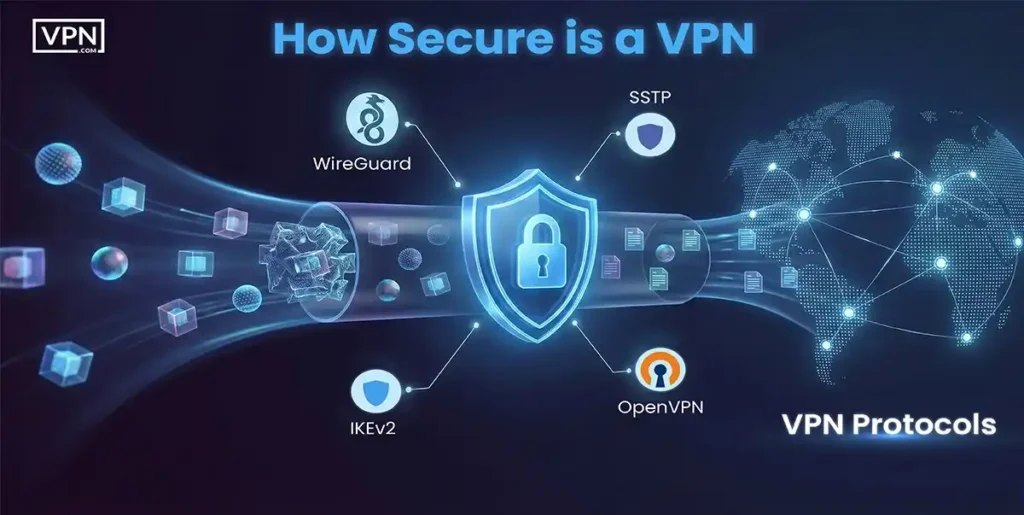
VPN security sparks a lot of debate among IT experts and people in the field. No two VPN services offer exactly the same level of protection or features. Two main things explain why differences exist.
- The first is the type of VPN technology the provider chooses to use. Each technology comes with its own strengths and built-in limits.
- The second involves legal and policy rules. The laws in the country where the VPN company is based and where its servers sit play a big role. The company’s own privacy rules also shape what they can and will do with that technology.
These factors together decide how secure and private a VPN service really becomes. Let’s look closer at both of them.
VPN Protocols
VPN protocols determine how a VPN service transmits your data. The most common ones you will see are PPTP, L2TP, SSTP, IKEv2, and OpenVPN. Let us give you a quick look at each so you can understand their strengths and weaknesses.
| VPN Protocol | Security Level | Speed | Key Notes | Recommendation |
| PPTP | Very Low | Fast | Old Microsoft protocol & very weak today | ❌ Not recommended |
| L2TP/IPsec | Moderate | Slow | Uses keys + IPsec but has known issues | ⚠️ Use with caution |
| SSTP | High | Moderate | Microsoft SSL/TLS & Good on Windows | ✅ Good option |
| IKEv2 | Very High | Fast | Strong and stable, especially on mobile | ✅ Highly recommended |
| OpenVPN | Very High | Moderate | Open-source, trusted, flexible, secure | ✅ Trusted standard |
| WireGuard | Very High | Very Fast | Modern, lightweight, advanced | ⭐ Best overall |
Most VPN services let you pick which protocol to use. The safer ones, like OpenVPN or IKEv2, make your entire session more protected. Sadly, not every device supports every protocol. Since Microsoft built most of them, Windows computers handle them all without trouble.
Encryption Basics
Encryption basics are pretty straightforward when you break them down. Here is how it works in simple steps.
- It starts with your normal readable data, also called plain text.
- Then a secret key gets applied to scramble that data in a careful way.
- What you end up with is encrypted data that looks like complete nonsense.
Only someone who has the exact same key can turn that scrambled mess back into the original readable information. All modern encryption follows this basic idea. The scrambling step uses very clever, complex math that experts have studied for years.
What really matters for you is that your data gets protected with the AES algorithm at 128 bits or stronger. Many leading VPNs take it further and use AES-256 encryption. Good examples include NordVPN, Surfshark, and ExpressVPN. As we discussed earlier, WireGuard relies on up-to-date encryption methods designed to stay secure while moving fast.
It usually uses ChaCha20 encryption, which serves as a modern choice instead of AES. Experts see ChaCha20 as very safe, and it often performs better, especially on phones and other mobile devices. Your VPN might have strong security overall, but the real protection depends on the protocol you choose and the exact encryption it uses to protect your information.
Legal Constraints and Our Vision
(Note: None of this counts as legal advice. Read it just for interest.)
Every solid VPN company works hard to guard your data, your privacy, and your safety online. Even so, they must follow the laws of the country where they are based. Those laws can limit what they do.
Depending on local rules, the government might force the company to hand over any records it holds about your activity through a court order. Sometimes countries have agreements to share this kind of information across borders. If you look carefully, you can find a VPN based in a country that has no such sharing deals with your own country.
Is it Legal to Use a VPN?
In short, yes, but not in every case. This guide explains VPN legality by country.
VPN technology is still fairly new in legal terms, so many countries have not fully updated their rules yet. This leaves things unclear and open to different interpretations.
In most places, VPNs are perfectly fine to use. You can use them without worry in the United States, Canada, the United Kingdom, and nearly all of Western Europe. What counts most is where your body is physically located when you connect.
On the other hand, several countries either ban VPNs or severely restrict them. These include China, Turkey, Iraq, the United Arab Emirates, Belarus, Oman, Russia, Iran, North Korea, and Turkmenistan.
In some nations, the VPN itself might be legal, but what you do with it matters. For example, using a VPN to torrent files or access content blocked by government rules can get you in trouble, even if having the VPN is okay. Check your local laws carefully, especially if you live in a country with heavy internet monitoring or censorship. To get clear answers for your own country, look up your government’s official rules.
Does a VPN Make Me Fully Anonymous Online?
No, a VPN does not make you fully anonymous online. But it still does a very good job of hiding a lot about you.
Without a VPN, your connection stays completely open. Your ISP, the public Wi-Fi router servers along the path, or anyone with the right skills can see your data clearly. A VPN fixes most of that. It encrypts everything you send and makes it appear that the VPN server is connecting, not your device.
To figure out how much anonymity you really get, look into these points.
- Does the service keep any logs of your activity?
- Where is the VPN company based? Some countries force companies by law to hold records. What happens if the government asks for information?
- Does the service save payment details? Do those details link back to you personally?
- Does it use strong encryption and a safe connection protocol?
The best VPN can boost your anonymity quite a bit, but it never gives total invisibility. If the provider keeps logs or sits in a country with strict data rules, someone could still trace your actions. Picking a VPN with a true no-logs policy and solid encryption, like what WireGuard offers, makes your privacy much stronger.
Also, make sure it blocks DNS leaks and WebRTC leaks. Those can reveal your real IP address even while you are connected. Not every VPN handles these things equally well. Choose carefully, and you can cover most of the risks we just talked about.
VPN Logging Policies
The logs your VPN provider keeps play a big role in how much real anonymity and privacy you actually get. Here are the main types of logs they might hold:
- User activity
- IP addresses
- Connection and disconnection times
- Devices you use
- Payment records
Any of these logs reduces your anonymity a little. Your original IP address can be linked to a specific browsing session. Connecting that session directly to your real identity takes effort and determination, but a determined agency could still manage it.
The fewer logs a provider keeps, the better your privacy becomes. A true no-logs policy stands as the best choice. Be cautious, though. Many VPNs promise strong privacy in their ads and on their websites. You must read the actual privacy policy to see the fine print and learn exactly what data they collect.
Some say their country has no data retention laws, but they stay quiet about their own logging habits. If online privacy matters to you, then pick the best VPN with a clear no-logs policy. WireGuard brings a modern protocol known for better security and speed. It also opens the door to stronger privacy by avoiding the need to keep extra logs.
Still, check if your provider actively watches or records your activity even when you use something advanced like WireGuard.
Free VPN Versus Paid VPN
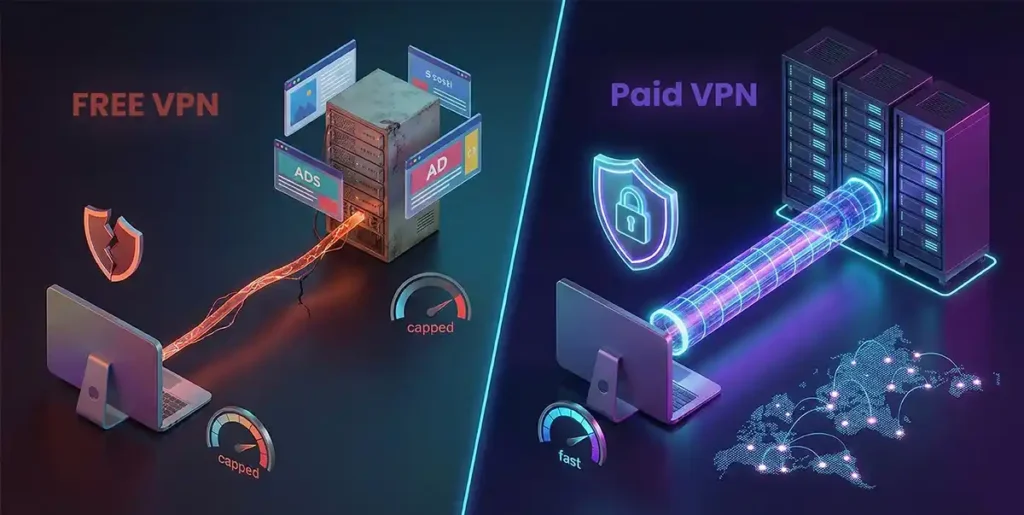
Running a solid best VPN service takes real money. Think about strong servers, constant data flow, big infrastructure staff salaries, and more. When a VPN is completely free, you have to ask what they give up to offer it. Do they log your activity for their own benefit? Do they push ads into your browsing? Could they sell your browsing data to someone else?
| Factor | Free VPNs | Paid VPNs |
| Cost | Free | Low monthly cost ($3–$5) |
| Business model | Ads, data logging, or data sales | Subscription-based |
| Privacy | Often logs user activity | Strict no-logs policies |
| Speed | Slow and throttled | Fast and consistent |
| Server access | Very limited | Large global network |
| Ads | Common | None |
| Data limits | Often capped | Unlimited |
| Security | Basic or weak | Strong encryption (WireGuard, OpenVPN) |
| Reliability | Unstable connections | Stable and dependable |
How to Test if Your VPN is Working?
Testing if your VPN is working is easy and important. It confirms that your real IP stays hidden, your DNS requests route through the VPN, and your speed holds up reasonably well.
Let us walk you through how to test your VPN with three quick checks you can do yourself:
First, Do An IP Check
Turn off your VPN and visit a site like ipleak.net or whatismyipaddress.com. Note your real IP address and location. Now connect to your VPN, preferably a server in another country. Refresh the page. The site should show the VPN server’s IP and location instead of yours. If it still shows your original details, your VPN has an IP leak and isn’t hiding your IP properly.
Next, Run a DNS Leak Test
DNS leaks occur when your device resolves domain names outside the VPN tunnel, revealing your IP address to your ISP. Go to dnsleaktest.com or ipleak.net with your VPN off to see your default DNS servers, which are usually provided by your ISP.
Connect the VPN and run the test again, usually the extended version. The results should list only DNS servers from your VPN provider or none tied to your ISP. If your ISP’s servers appear, there is a leak, and your privacy is at risk.
Finally, Check Your Speed
Use a tool like speedtest.net or fast.com before and after connecting to the VPN. Expect a drop due to encryption and routing, often 10-30 percent. A huge slowdown might mean picking a closer server, trying the WireGuard protocol, or switching providers. Good VPNs keep speeds solid for streaming, gaming, or downloads.
Run these tests right after setup, after updates, or if something feels off. Most top VPNs, like those with WireGuard, block leaks well but always verify. If you spot issues, try a different server, restart the app, or contact support. Stay safe out there.
How Much Does a VPN Cost?
The average price across popular VPNs comes to about $4.99 per month. That number shows you this is usually a small expense. VPNs that charge more than $15 a month are rare. There is rarely a good reason to pick one since plenty of strong and affordable options exist.
Most providers offer large discounts when you commit to a longer plan, like two or three years, instead of paying month by month. For example, NordVPN, which we really like, costs $12.99 per month. But their two-year plan drops to just $3.39 per month. That works out to a 70 percent savings.
Even though prices remain low, a good premium VPN often offers better features. You get things like WireGuard support, a true no-logs policy, quicker speeds, and servers spread around the world. Over time, paying for a service that truly focuses on your privacy and security makes sense as a smart investment.
Can I Use a VPN for Torrenting?
(Note: None of this counts as legal advice. Read it just for interest.)
Yes, but it depends on the VPN service you pick and exactly what files you are torrenting.
People call torrenting a specific way to share and download files over the internet. The method itself is neutral. It becomes legal when you transfer files you own or have permission to share. Piracy stays illegal no matter what tool you use, even with a VPN.
Next, look at the VPN provider’s rules on torrenting. Most good-quality services allow it without problems. From our checks, you can torrent safely with popular choices like NordVPN, ExpressVPN, Surfshark, and PIA. When you choose a VPN for torrenting, focus on one that does not log your activity. Services that support WireGuard often give you stronger security and quicker speeds, which helps a lot with torrenting.
Look for providers that offer dedicated P2P servers optimized for fast downloads, plus strong encryption to keep trackers at bay. A kill switch matters too. It cuts your internet right away if the VPN drops, so your real IP address never leaks during a torrent session. Security for torrenting really hinges on the VPN’s logging policy and whether it shares user data. If a VPN keeps no logs in general, it also keeps none for your torrenting.
Download speed plays a big role as well. It can be tricky to know the real speeds before you sign up. We ran our own tests and based on the results, we recommend NordVPN, ExpressVPN, and PIA for their strong download performance during torrenting.
Can I Use a VPN to Watch Netflix and Hulu?
You can, but just like many other things on this list, it depends on which VPN you choose.
Netflix now reaches more than 190 countries, yet not every show appears everywhere. Old licensing deals made before Netflix went global give local TV stations rights to some shows, even ones Netflix created. Those deals prevent Netflix from legally showing the content in certain places.
The rules get complicated, but a VPN offers a simple way around them. Netflix and Hulu limit content based on your location. If you are in a country where a show is blocked, you cannot watch it. A VPN solves this easily. You pick a server in any country you want.
Connect to one where the show is available, and Netflix or Hulu sees you there instead of your real spot. That is really all it takes. Keep in mind, Netflix and Hulu keep getting better at spotting and blocking VPNs, especially for geo-restricted shows. VPN companies fight back by continually updating their methods.
Providers like NordVPN and ExpressVPN that support WireGuard usually perform better when you try to avoid these blocks.
When to Use a VPN & When Not to Use a VPN?
There are a number of good reasons to use a VPN, and as predictable as this may sound, we really see no good reason not to use a VPN if you’re taking your online security and privacy seriously.
| Situation | Use a VPN? | Why |
| Browsing privacy matters | ✅ Yes | Encrypts activity and hides it from ISPs and third parties |
| Using public Wi-Fi | ✅ Yes | Protects against hacking and unsecured networks |
| Accessing geo-blocked content | ✅ Yes | Hides the location to unlock restricted platforms |
| Streaming or torrenting | ✅ Yes | Improves access and adds privacy protection |
| Gaming or HD streaming | ✅ Yes | WireGuard delivers fast speeds with strong encryption |
| Traveling or digital nomad work | ✅ Yes | Secures connections across different networks |
| Concerned about anonymity | ✅ Yes | Masks the IP address and reduces tracking |
| Very slow internet connection | ⚠️ Maybe | VPN may slightly reduce speed on poor networks |
| Using outdated VPN protocols | ❌ Avoid | Older protocols cause noticeable slowdowns |
Frequently Asked Questions
What is a VPN, and Why Do I Need It?
A VPN is a tool that creates a secure and encrypted tunnel for your internet traffic. It hides your real IP address and scrambles your data. You need it to stay private from your ISP, hackers, or trackers. Protect yourself on public Wi-Fi, stop bandwidth throttling, and unlock content blocked in your area.
How Do I Turn On a VPN?
Download and install the app from your chosen VPN provider. Open the app, sign in if needed, pick a server location, and tap the big connect button. On phones, it usually appears as a quick toggle in settings after you add the VPN profile.
How Do I Know If I Have a VPN?
Check your device settings. On Windows, go to Network & Internet, then VPN. On iPhone, go to Settings > General > VPN & Device Management. On Android, check Settings > Network & internet> VPN. If you see an active connection name or icon in your status bar, then you have a VPN running.
Should VPN Be On or Off?
Keep it on most of the time, especially on public Wi-Fi when you want privacy or need to access restricted content. Turn it off only if a site or app blocks VPNs or if you need your real local speed for something specific, like certain banking apps.
What is the Difference Between VPN Protocols like WireGuard and OpenVPN?
WireGuard is newer, lighter, faster, and uses modern cryptography, so it gives great speed with strong security. OpenVPN is older but very trusted, flexible, and widely supported with excellent security. Choose WireGuard for quick performance, especially on phones. Pick OpenVPN if you need maximum compatibility or extra customization.
How Do I Know if My VPN is Actually Working?
Visit a site like ipleak.net or whatismyipaddress.com. It should show the VPN server’s IP location and country, not your real one. Also, check for no DNS leaks and confirm that your traffic stays encrypted. Most good VPN apps show a green connection status when everything works.
Can My Internet Service Provider Still See My Internet Activity When I Use a VPN?
No, they cannot see what sites you visit, what you download, or the content of your traffic. They only see encrypted data sent to the VPN server, along with how much data you use. A no-logs VPN keeps even that detail private from them.
How Do I Choose a VPN That is Fast Enough for My Needs?
Look for providers with WireGuard support, many nearby servers, and good reviews for speed. Test with a money-back guarantee. Check real-user speed tests for your region. Services like NordVPN, ExpressVPN, or Surfshark usually rank high for consistent fast performance, even during streaming or downloads.
What is a Dedicated IP Address, and Do I Need One?
A dedicated IP is a fixed address that you use instead of sharing it with many people. It helps avoid CAPTCHA triggers, makes remote work logins easier, and reduces blocks on some services. Most people do not need one unless they face frequent verification issues or need steady access for business tools.
How Does a VPN Affect My Online Gaming Experience?
It can lower ping if you connect to a closer or less crowded server, and it stops ISP throttling during heavy play. But it might add slight latency if the server is far away. Choose a fast protocol like WireGuard, pick nearby servers, and use split tunneling to keep game traffic direct when possible.
Can I Use a VPN On My Work or School Network?
Usually, yes, but check their rules first. Many workplaces and schools block VPNs or log heavy use. If allowed, it helps protect your privacy on shared networks. Just know they might still see you connecting to a VPN server even if they cannot see inside the tunnel.
Does a VPN Hide My Location from Websites?
Yes, websites see the VPN server’s location and IP instead of yours. This lets you appear in another city or country, which unlocks region-locked content and hides your real whereabouts.
How Do I Use a VPN to Avoid Censorship in a Restrictive Country?
Choose the best VPN with obfuscated servers or stealth features that hide VPN traffic, so it appears as normal browsing. Connect to a server outside the restricted area, preferably nearby for speed. Use WireGuard or OpenVPN with strong encryption. Test it before you travel and pick providers known to work well in places like China or Iran, such as ExpressVPN or NordVPN.
The Bottom Line
The best VPN gives you real control over your online privacy and security in a simple, powerful way. It encrypts your data, hides your real location from websites, and stops your ISP from tracking every move you make. We walked through how it works, why public Wi-Fi becomes safer, how it unlocks blocked shows, ends throttling, and protects remote work.
Modern options like WireGuard bring fast speeds, strong security, and clean performance without old weaknesses. A good no-logs paid VPN from a privacy-friendly country cuts most risks while keeping things quick and reliable. No tool makes you 100 percent anonymous, but the best VPN slashes surveillance tracking and leaks dramatically.
Free ones often trade your privacy for ads or logs, so the small monthly cost for a trusted service makes sense. If you value privacy, browsing freedom, and online safety, a quality VPN fits right into your daily routine.