Best VPN for Enterprise: Tested and Ranked for Business
The best VPN for enterprise does more than encrypt traffic. Compare our top picks by security depth management tools and compliance support right now.
Bottom Line: Consumer VPNs can’t handle the sprawling attack surface of enterprise environments — the right enterprise VPN adds centralized management, compliance tooling, and security depth that scales across distributed teams and branch offices.
Enterprise teams operate across home offices, coworking spaces and branch locations spanning multiple time zones. That sprawl creates an attack surface that consumer VPNs cannot address.
For a broader overview of business VPN options, see our best VPN for business guide. Choosing the right enterprise VPN touches compliance, productivity, IT overhead and incident response.
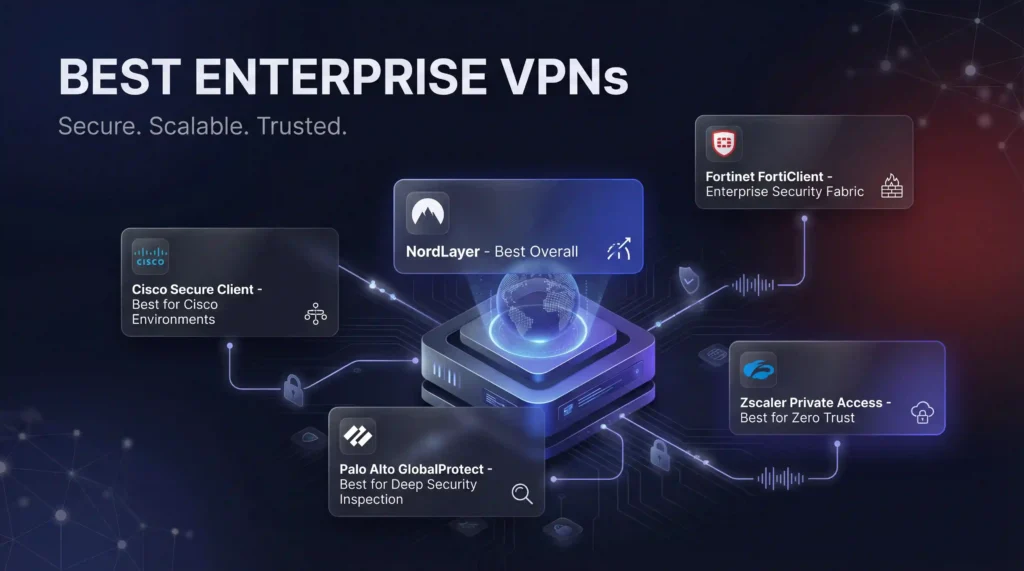
Best VPN for Enterprise (Quick Picks)
- Best Overall: NordLayer
- Best for Cisco environments: Cisco Secure Client
- Best for deep security inspection: Palo Alto GlobalProtect
- Best for Zero Trust: Zscaler Private Access
Top Enterprise VPN Solutions
We evaluated the leading enterprise VPN platforms based on security depth, management tools, protocol support, compliance capability, performance and independent user reviews.
| Provider | Best For | Key Differentiator |
|---|---|---|
| NordLayer | Cloud-first enterprises | SSO, SCIM, NordLynx protocol |
| Cisco Secure Client | Cisco environments | Pre-connection compliance checks |
| Palo Alto GlobalProtect | Deep security inspection | Real-time traffic inspection via App-ID |
| Fortinet FortiClient | Hardware-accelerated performance | Unified VPN, firewall and endpoint protection |
| Zscaler ZPA | Zero Trust | App-level access, no network exposure |
NordLayer
Best for cloud-first enterprises and hybrid teams. AES-256 encryption with NordLynx protocol, SSO integration (Azure AD, Okta, Google Workspace), SCIM-based provisioning, device posture checks and DNS filtering. Speeds reach 237 Mbps down and 221 Mbps up.
Cisco Secure Client
Best for large enterprises with existing Cisco infrastructure. Runs pre-connection device compliance checks and blocks non-compliant devices before the tunnel opens. Split tunneling is disabled by default, keeping all traffic within the corporate security stack.
Palo Alto GlobalProtect
Best for security-first organizations needing deep traffic inspection. Connects to Palo Alto’s next-generation firewall and Prisma Access cloud platform. Inspects all traffic continuously using App-ID, User-ID and real-time content inspection.
Fortinet FortiClient
Best for enterprises needing hardware-accelerated performance with built-in endpoint protection. Unifies VPN, firewall, endpoint protection and threat intelligence under one management plane. Supports IPSec and SSL tunneling. Free trial available.
Zscaler Private Access (ZPA)
Best for cloud-native enterprises committed to Zero Trust. Connects users directly to specific applications without exposing the underlying network. Application IPs remain invisible to the public internet. Cloud-only heavy on-premises environments will need a phased approach.
Zero Trust: The Shift Beyond Traditional VPN
Traditional remote access VPNs grant broad network access once a user authenticates. If credentials are stolen, attackers inherit that same access. Zero Trust Network Access (ZTNA) inverts this model: every request is untrusted until verified and users only reach the specific applications their role requires. Device health, identity, location and behavior are evaluated continuously, not just at login.
Over 70% of new remote-access deployments now use ZTNA instead of traditional VPN, up from under 10% in 2021.
How to Choose the Best VPN for Enterprise?
Choosing the right enterprise VPN starts with matching your requirements to platform strengths:
- Map security priorities: Cloud application security favors ZTNA. Multiple physical offices need site-to-site VPN support.
- Confirm compliance alignment: Verify your platform supports HIPAA, PCI DSS, GDPR or whichever frameworks apply.
- Run a proof of concept: Deploy to 25–50 users before committing. Test reliability, failover and support responsiveness.
Final Verdict
NordLayer suits most organizations with fast deployment and ZTNA integration. Cisco Secure Client fits large Cisco shops. Palo Alto GlobalProtect serves security-first teams.
Zscaler ZPA works for cloud-heavy enterprises ready to eliminate the traditional VPN surface. With the average breach costing $4.56 million, deploying the wrong VPN costs far less than deploying none.
References
- https://www.pcmag.com/picks/the-best-vpns-for-businesses-and-teams
- https://www.techrepublic.com/article/top-enterprise-vpns/
- https://www.fortinet.com/resources/cyberglossary/enterprise-vpn-solutions
- https://www.comparitech.com/blog/vpn-privacy/corporate-enterprise-vpn/
- https://www.cisco.com/site/us/en/products/security/secure-client/index.html
- https://www.paloaltonetworks.com/sase/globalprotect